Such attacks do not target ordinary individuals, but rather specific members within a company or organization. The stolen information is far beyond what typical phishing attacks obtain—extending to highly sensitive data such as intellectual property, trade secrets, and most importantly, the control capabilities of privileged users. Once attackers impersonate these privileged accounts, they can easily and freely access critical assets. Therefore, implementing a robust privileged access management (PAM) system has become a top cybersecurity priority for enterprises.
In today’s IT environment, most access control policies managed by IT departments focus on general users performing routine tasks—such as internal employees. These policies cover account naming conventions, password rules, required password changes, login lockout thresholds, and more.
However, accounts with elevated system access—such as system administrators, network engineers, DBAs, application developers, or application service accounts—are often excluded from strict controls. Organizations hesitate to enforce stricter policies due to concerns that doing so may cause operational inconvenience or system downtime. As a result, privileged accounts are frequently treated as exceptions.
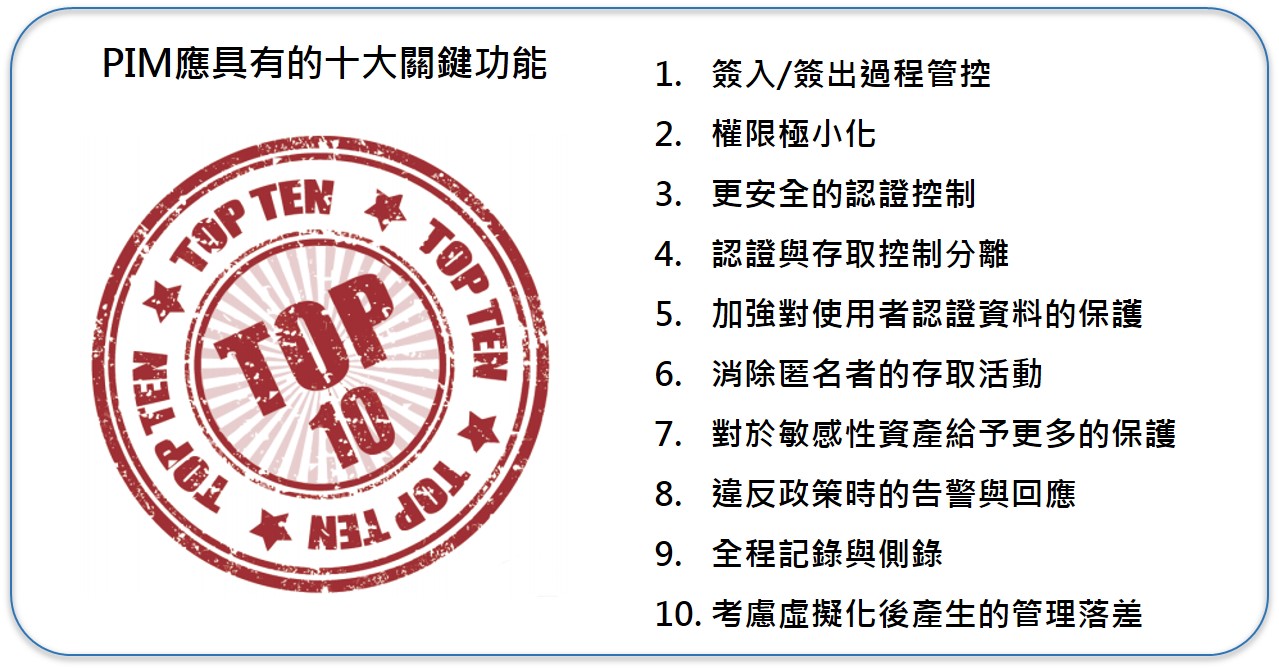
Yet, the greater the access privilege, the greater the potential impact. If a privileged account holder has malicious intent—such as stealing critical information or disrupting system operations—the consequences could be catastrophic. This is why establishing a privileged access management system aligned with enterprise needs has become an essential cybersecurity strategy.
When evaluating the adoption of a privileged management solution, it is recommended to consider two key perspectives: “before implementation” and “after implementation.” These serve as essential factors for preliminary assessment.
-
Privileged Identity Management
Aligned with privileged account management policies, the solution adopts a Zero Trust approach. Through an easy-to-use web interface that connects to a single, hardened secure gateway, it provides centralized access, session control, logging, and audit capabilities.
-
Password Management
This eliminates shared passwords and prevents spear-phishing or APT-style credential attacks. It enhances productivity for both privileged users and security teams. The solution also supports A2A password management to reduce the risk of exposed application credentials, and it integrates with existing or external password vaults to protect prior investments.
-
User Monitoring and Recording
The system records the entire privileged session, blocks unauthorized activities, and sends alerts to the SOC. Recorded sessions can be replayed, with policy-violating timestamps highlighted for quick review.
-
Access Control for Third-Party (Outsourced) Vendors
Regardless of where privileged users originate, the solution provides consistent control and monitoring. It centralizes all access through a single secure channel, ensuring stricter and safer privileged connections.
Solution :